Federal authorities have arrested and indicted a 20-year-old U.S. Army soldier on suspicion of being Kiberphant0m, a cybercriminal who has been selling and leaking sensitive customer call records stolen earlier this year from AT&T and Verizon. As first reported by KrebsOnSecurity last month, the accused is a communications specialist who was recently stationed in South Korea.

One of several selfies on the Facebook page of Cameron Wagenius.
Cameron John Wagenius, 20, was arrested near the Army base in Fort Hood, Texas on Dec. 20, after being indicted on two criminal counts of unlawful transfer of confidential phone records.
The sparse, two-page indictment (PDF) doesn’t reference specific victims or hacking activity, nor does it include any personal details about the accused. But a conversation with Wagenius’ mother — Minnesota native Alicia Roen — filled in the gaps.
Roen said that prior to her son’s arrest he’d acknowledged being associated with Connor Riley Moucka, a.k.a. “Judische,” a prolific cybercriminal from Canada who was arrested in late October for stealing data from and extorting dozens of companies that stored data at the cloud service Snowflake.
In an interview with KrebsOnSecurity, Judische said he had no interest in selling the data he’d stolen from Snowflake customers and telecom providers, and that he preferred to outsource that to Kiberphant0m and others. Meanwhile, Kiberphant0m claimed in posts on Telegram that he was responsible for hacking into at least 15 telecommunications firms, including AT&T and Verizon.
On November 26, KrebsOnSecurity published a story that followed a trail of clues left behind by Kiberphantom indicating he was a U.S. Army soldier stationed in South Korea.

An 18-year-old Cameron Wagenius, joining the U.S. Army.
Ms. Roen said Cameron worked on radio signals and network communications at an Army base in South Korea for the past two years, returning to the United States periodically. She said Cameron was always good with computers, but that she had no idea he might have been involved in criminal hacking.
“I never was aware he was into hacking,” Roen said. “It was definitely a shock to me when we found this stuff out.”
Ms. Roen said Cameron joined the Army as soon as he was of age, following in his older brother’s footsteps.
“He and his brother when they were like 6 and 7 years old would ask for MREs from other countries,” she recalled, referring to military-issued “meals ready to eat” food rations. “They both always wanted to be in the Army. I’m not sure where things went wrong.”
Immediately after news broke of Moucka’s arrest, Kiberphant0m posted on the hacker community BreachForums what they claimed were the AT&T call logs for President-elect Donald J. Trump and for Vice President Kamala Harris.
“In the event you do not reach out to us @ATNT all presidential government call logs will be leaked,” Kiberphant0m threatened, signing their post with multiple “#FREEWAIFU” tags. “You don’t think we don’t have plans in the event of an arrest? Think again.”
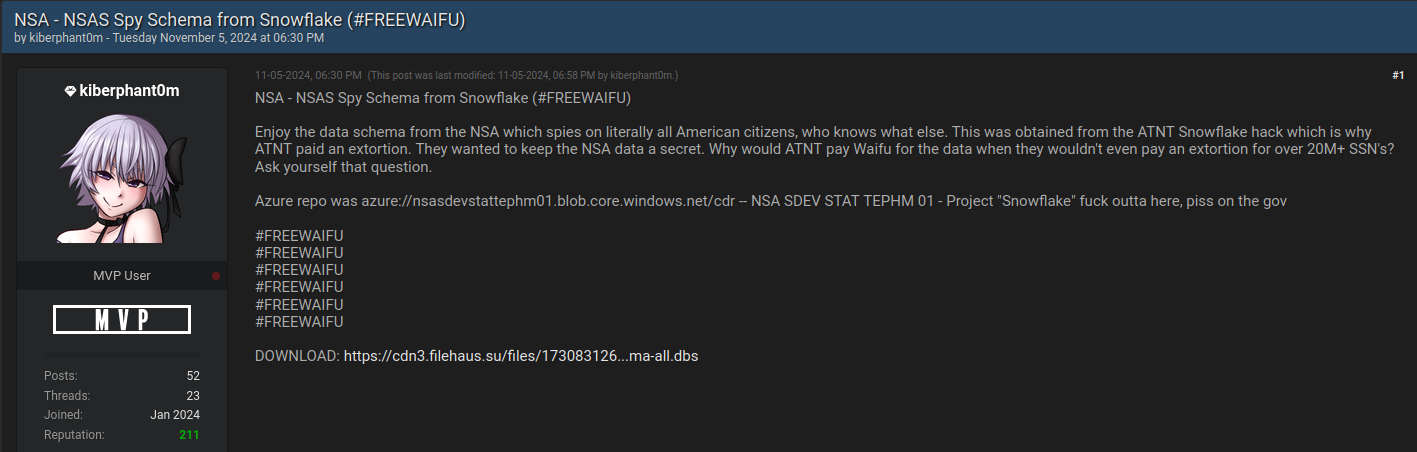
Kiberphant0m posting what he claimed was a “data schema” stolen from the NSA via AT&T.
On that same day, Kiberphant0m posted what they claimed was the “data schema” from the U.S. National Security Agency.
On Nov. 5, Kiberphant0m offered call logs stolen from Verizon’s push-to-talk (PTT) customers — mainly U.S. government agencies and emergency first responders. On Nov. 9, Kiberphant0m posted a sales thread on BreachForums offering a “SIM-swapping” service targeting Verizon PTT customers. In a SIM-swap, fraudsters use credentials that are phished or stolen from mobile phone company employees to divert a target’s phone calls and text messages to a device they control.
The profile photo on Wagenius’ Facebook page was deleted within hours of my Nov. 26 story identifying Kiberphant0m as a likely U.S. Army soldier. Still, many of his original profile photos remain, including several that show Wagenius in uniform while holding various Army-issued weapons.
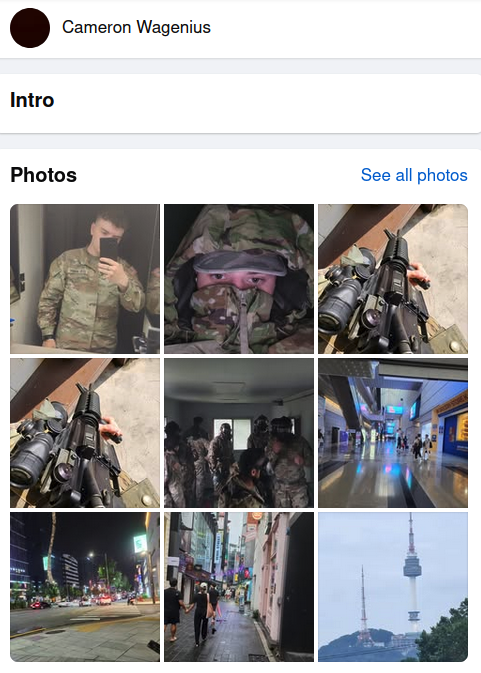
Several profile photos visible on the Facebook page of Cameron Wagenius.
November’s story on Kiberphant0m cited his own Telegram messages saying he maintained a large botnet that was used for distributed denial-of-service (DDoS) attacks to knock websites, users and networks offline. In 2023, Kiberphant0m sold remote access credentials for a major U.S. defense contractor.
Allison Nixon is chief research officer at the New York-based cybersecurity firm Unit 221B who helped track down Kiberphant0m’s real life identity. Nixon was among several security researchers who faced harassment and specific threats of violence from Judische and his associates.
“Anonymously extorting the President and VP as a member of the military is a bad idea, but it’s an even worse idea to harass people who specialize in de-anonymizing cybercriminals,” Nixon told KrebsOnSecurity. She said the investigation into Kiberphant0m shows that law enforcement is getting better and faster at going after cybercriminals — especially those who are actually living in the United States.
“Between when we, and an anonymous colleague, found his opsec mistake on November 10th to his last Telegram activity on December 6, law enforcement set the speed record for the fastest turnaround time for an American federal cyber case that I have witnessed in my career,” she said.
Nixon asked to share a message for all the other Kiberphant0ms out there who think they can’t be found and arrested.
“I know that young people involved in cybercrime will read these articles,” Nixon said. “You need to stop doing stupid shit and get a lawyer. Law enforcement wants to put all of you in prison for a long time.”
The indictment against Wagenius was filed in Texas, but the case has been transferred to the U.S. District Court for the Western District of Washington in Seattle.
